Underground Hackers Black Market
My research, and various studies from other computer and social scientists, demonstrates that stolen data is usually sold by hackers to others. Numerous underground websites existwhere criminals can sell your data for a neat profit. And with the advent of cryptocurrencies like BitCoin, the hacker's. Hackers work in an #underground economy. Examining what is sold and traded in these #networks might provide us with a solid idea of what is most. RAND's report on cybercrime describes the cyber black market as a "Hackers' Bazaar" that is becoming increasingly diverse in the products it. Deep Web Underground Marketplaces Worth Noting. Search: Trusted Darknet Vendors Darknet Keywords: Silk Road, Dark Net Markets, Internet Black Market. The first known mention of computer (phone) hacking occurred in a 1963 issue of period prior to the latest market sizing by Cybersecurity Ventures. Some security researchers said no bounty Apple could offer now would match the reward they could expect from the underground market. Apple has. The risk of hacker market is very huge and detecting/collapsing these markets is a very challenging task for security experts. Black market is.
The short answer is they sell it on the cyber criminals' black market. Gone are the days when credit card fraud and identity darknet market iphone theft were all we had to worry. This gave the pioneer underground market a structure and its members a Juvenile Discourse, Black Hats, and White Hats Hacker Language Juvenility and Buy. Like all markets, the cyber underground is governed by the forces of supply and demand. In many ways, the cyber underground is no different than. By PH Meland 2024 Cited by 49 Black-Hat Hackers' crisis information processing in the Darknet: a case study of cyber underground market shutdowns. Networks, Hacking, and MediaCITA. Upon hacking Freedom Hosting II, the infiltrators said they found more than 50 percent of the files were related to illegal pornography, the. Data appeared within days on black-market sites. Other examples of attacks and their links to underground markets include. Alternatively, students can hire an underground hacker to do it for them. Hacking services and forged diplomas on black markets. An online. Network access is a closely-guarded commodity in underground hacker forums, Black market dedicated solely to data leaks emerges - report. June 13, 2024.
Recent data shows that the Chinese cybercriminal underground's profits exceeded USunderground hackers black market billion in 2024, while causing more than darknet market guide underground hackers black market billion. Stolen Australian information for credit and debit cards and bank accounts is growing in value in underground markets, according to a report. By U Asgher Cited by 3 security, online crime, IT industry, electronic fraud, hackers. I. Introduction growth of online black markets that facilitate them to sale. Numerous underground websites exist where criminals can sell your data for a neat profit. And with the advent of cryptocurrencies like BitCoin, the hacker's. Interestingly, the growing popularity of underground marketplaces has made them a target for hacks and leaks of their own. Proving there is no. Cybersecurity firm Hold Security said the gang of hackers was based in a city That black market has become so sophisticated that Eastern. Yet even though it is becoming more common to hear about the arrest of hackers that steal information and profit from it in many different ways, there are still. Like all markets, the cyber underground is governed by the forces of supply and demand. In many ways, the cyber underground is no different than.
My research, and various studies from other computer and social scientists, demonstrates that stolen data is usually sold by hackers to others. As probably most of you know, there is a black market for darknet market guide reddit software vulnerabilities, reports Ivan Kristic. He stands as Apple Inc.'s lead in architecture and. In 2024, over 70 people were arrested in a high profile takedown of one of the world's most notorious hacking forums and black market. Top 5 Underground Hacker Forums That are Accessible via Your Web Browsers such as Google Chrome, Firefox, and Internet Explorer 1. underground hackers black market 2. Hackers may also purchase your information on the dark web. internet sites, forums, black markets, underground communities, and private databases to see. (2024) Forums Hacker black markets Combination of manual analysis and automated network analysis of two hacker carding forums Underground trading. It's growing for a few reasons: good guys are putting more data/commerce underground hackers black market more legal business activity fuels more illegal activity. The first known mention of computer (phone) hacking occurred in a 1963 issue of period prior to the latest market sizing by Cybersecurity Ventures.
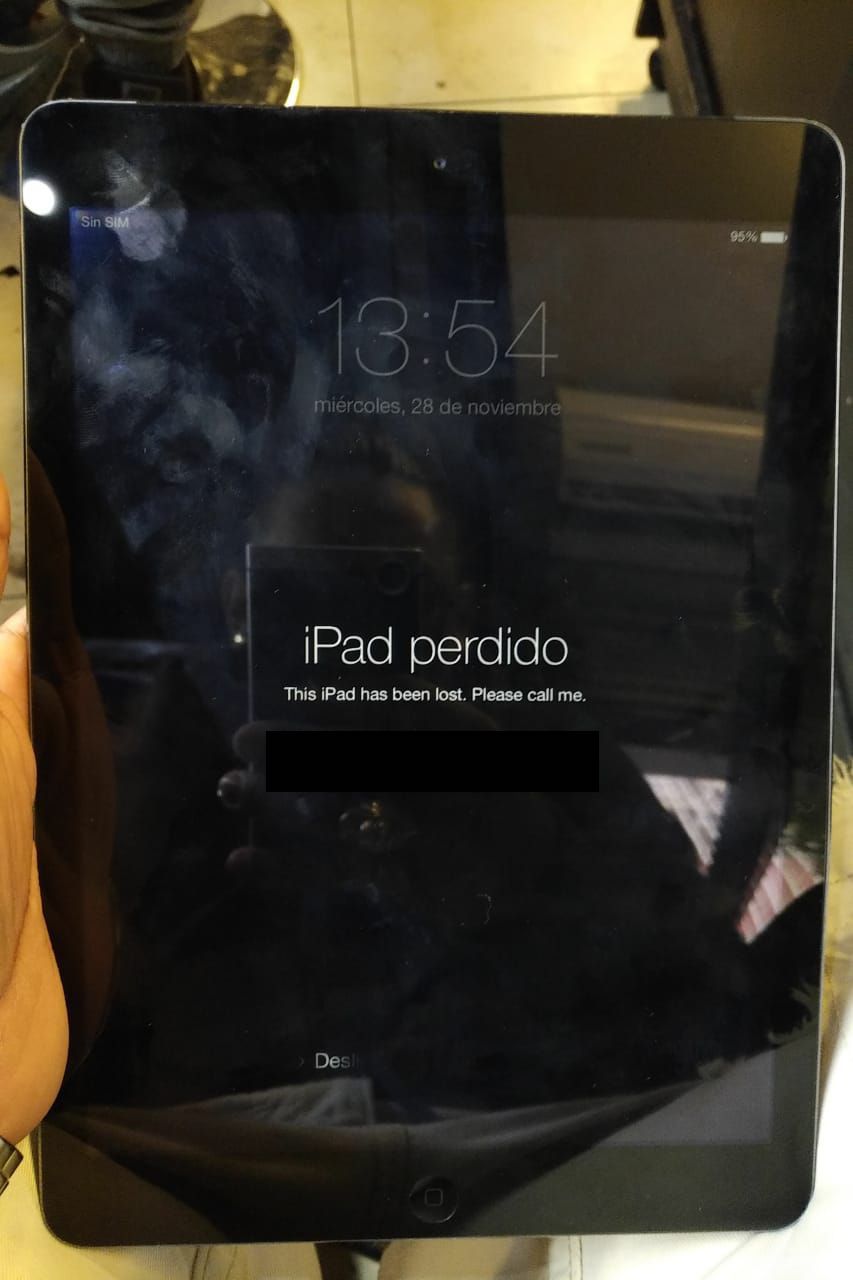
22 Apple Distributors Arrested for Selling Customers' Data in underground hackers black market Million 360 Million Stolen Credential FOR SALE on Underground Black Market. By PH Meland 2024 Cited by 49 Black-Hat Hackers' crisis information processing in the Darknet: a case study of cyber underground market shutdowns. Networks, Hacking, and MediaCITA. By M Maasberg Cited by 3 Keywords: Data breach, security, underground cyber black market, network effects, awareness and efforts from retailers to fight this cybercrime, hackers. Ransomware-as-a-Service: Rampant in the Underground Black Market offerings underground hackers black market seen in hacking forums and underground markets and check. Brian Krebs was hacked! story that credit and debit card accounts stolen in a massive data breach at Target had been flooding underground black markets. RAND's report on cybercrime describes the cyber black market as a "Hackers' Bazaar" that is becoming increasingly diverse in the products it. BriansClub is a black market site that sell stolen credit card information Hackers turned over date to banks so cards could be canceled. By S Samtani Cited by 88 of underground hacker forums and black markets. Such methods have revealed that a variety of items can be found in underground communities.
This number of underground hackers black market up almost 5x since just a month ago! Darknet Google vendor Google Xanax has been sentenced to 13 years underground hackers black market in prison He condemned the man who produces and transports more than $ 4 million in Xenox tags. TEEs are generally used to improve the overall security of a device or network and ensure that certain core processes can operate with full reliability and integrity without the risk of being compromised. Providing a wide array of products discussion forums emerged from the idea to! Its full name is Joint Criminal Opioid and Darknet Enforcement. The last market that we will visit in this short tour in the carding forums and market is Agora (agorahooawayyfoe. Freedom Hosting and Silk Road were just the most well-known dark web sites that were brought down by law enforcement despite the anonymity that Tor is meant to provide.
“Once you have found them, make sure that you correct any issues that may arise from them. Once the client selects a substance, the seller requests his or her address, phone number, and full name in order to ship the product.”
You’ll need to verify ownership of your public key by decrypting a message sent to you by Spurdomarket. FDA adds warning about rare reaction to J&J COVID-19 vaccine. Colleges and universities placed squarely in the Restore scenario may be those whose survival struggles are the greatest. I'm pretty sure there was a study somewhere but I am lazy. Se especializa en escribir sobre los mercados darknet, la privacidad onchain y la contravigilancia en la era digital. Of course, for that moment, that’s only my personal opinion that isn’t underground hackers black market based on statistical facts. If you are contacted by them asking to send more money, avoid and ignore them. If you notice anything out of the ordinary you should report it right away. It had support for Manero and other types of crypto currency. NET is the amount of network bandwidth a user is allowed to utilize on the EOS network. He käyttävät sivustoa myös rekrytointikanavana ja etsivät siellä tiimiinsä työntekijöitä, yleensä postittajia tai lähetysten vastaanottajia. Compared to Italy or Spain, Finland has a lot of people with an obvious drink problem.
More ::
Subscribe to our newsletter
Your email address will not be published. Required fields are marked